Computer networking is the backbone of our interconnected world, enabling devices to communicate and share information seamlessly. In this digital era, where information flows at the speed of light, understanding the essence of networking is paramount.
What is Networking?
At its core, computer networking involves the interconnection of multiple devices, such as computers, servers, and smartphones, to facilitate data exchange and communication. These connections can be local, spanning a room or a building, or global, connecting devices across continents.
Historical Perspective
The roots of computer networking can be traced back to the 1960s when the ARPANET (Advanced Research Projects Agency Network) laid the foundation for the modern internet. Over the decades, networking technologies have evolved, leading to the sophisticated systems we rely on today.
How Does Networking Work?
Data Transmission
Data is broken down into packets and sent across the network. These packets travel through various network devices, following the best path to reach their destination.
Routing and Switching
Routers determine the most efficient path for data packets, while switches manage the flow of data within a local network.
- Devices: At the core of networking are devices such as computers, smartphones, tablets, and servers. Each of these devices has a unique identifier called an IP (Internet Protocol) address, which is like their digital home address on the network.
- Data Packets: When you send or receive information over a network, it’s broken down into smaller units called data packets. These packets contain both the data being transmitted and information about where it’s going and where it came from.
- Network Hardware: The physical infrastructure of a network includes various hardware components. These include routers, switches, and access points.
- Router: The router is a central device that connects different networks, such as your home network to the internet. It directs data packets between devices within your network and those on external networks, like websites or other servers.
- Switch: Switches are used to connect multiple devices within the same network. They determine how to forward data packets within the network, ensuring they reach their intended destination efficiently.
- Access Point: Access points are used in wireless networks (Wi-Fi) to allow devices to connect wirelessly to the network. They act as a bridge between wireless devices and the wired network.
- Protocols: To ensure devices can understand each other, they follow a set of rules and conventions known as protocols. The most common protocol used on the Internet is the Internet Protocol (IP). IP is responsible for addressing and routing packets of data so they can travel across networks and reach their intended destination.
- DNS (Domain Name System): While devices use IP addresses to communicate, humans find it easier to work with domain names (like www.example.com) instead of remembering numerical IP addresses. DNS translates these domain names into IP addresses, allowing you to access websites using friendly names.
- Firewalls and Security: Security is a critical aspect of networking. Firewalls are used to protect networks by filtering incoming and outgoing traffic based on predefined security rules. Additionally, encryption is often employed to secure data as it travels across networks, making it unreadable to unauthorized users.
- Routing and Data Transfer: When you send data over a network, your device packages the information into data packets. These packets are then routed through various network devices like routers and switches, following the most efficient path to their destination. This might involve multiple intermediate devices and networks, especially when communicating over the internet.
- Destination and Acknowledgment: At the destination, the receiving device reassembles the data packets in the correct order and acknowledges their receipt. If any packets are lost or corrupted during transmission, the receiving device may request retransmission.
- Two-Way Communication: Networking isn’t just about sending data; it’s also about receiving responses. Devices engage in a two-way conversation, where they send data packets and receive responses from other devices. This allows for real-time interactions, like video calls or online gaming.
- The Internet: The Internet is a global network of networks that connects billions of devices worldwide. It’s made up of many interconnected routers and switches, allowing data to travel across vast distances, often through numerous intermediaries, to reach its final destination.
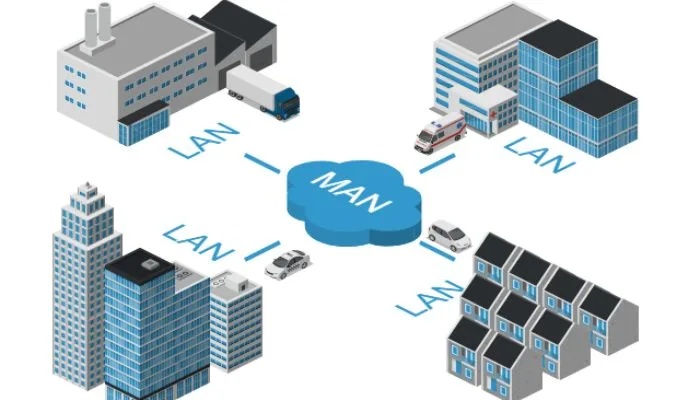
Types of Computer Networks
Local Area Network (LAN)
LANs are confined to a limited geographical area, typically within a single building or campus. They are commonly used in homes, offices, and educational institutions to connect devices for resource sharing and communication.
Wide Area Network (WAN)
In contrast to LANs, WANs cover larger geographic areas, often spanning cities, countries, or even continents. The internet itself can be considered a vast WAN, connecting people and resources globally.
Wireless Networks (Wi-Fi)
Wi-Fi networks have revolutionized connectivity by eliminating the need for physical cables. They enable wireless communication between devices, making it possible to access the internet from virtually anywhere.
Key Components of Computer Networking
- Network Devices: Network devices are the hardware components that facilitate communication between devices. Examples include routers, switches, and modems, each with its unique role in managing data traffic.
- Network Protocols: Protocols are a set of rules and conventions that govern how data is transmitted and received over a network. TCP/IP (Transmission Control Protocol/Internet Protocol) is the foundation of Internet communication.
Why is networking important?
- Communication: Networking enables seamless communication among devices, computers, and users across various geographical locations. It facilitates the exchange of information through emails, messaging apps, voice and video calls, and more. This connectivity has revolutionized how individuals and businesses interact.
- Data Sharing: Networking allows the sharing of data and resources among devices. This is essential for collaborative work in businesses and institutions. It also enables file sharing, which is integral to everyday tasks and activities.
- Access to Information: The internet, which is a global network of networks, provides access to a vast repository of information. Networking empowers individuals to access news, research, education, and entertainment resources easily. It has democratized information, making knowledge accessible to a global audience.
- Remote Work and Telecommuting: In recent years, networking has become indispensable for remote work and telecommuting. It enables employees to work from anywhere, promoting flexibility and work-life balance. This has become particularly vital during global events such as the COVID-19 pandemic.
- Business and Commerce: Networking plays a pivotal role in modern commerce. It allows businesses to connect with customers, suppliers, and partners. Online marketplaces, e-commerce websites, and digital payment systems all rely on robust networking infrastructure.
- Innovation and Technology Advancement: Networking fosters innovation by connecting researchers, developers, and innovators worldwide. This collaboration leads to the creation of new technologies, applications, and services that improve our quality of life.
- Entertainment and Social Interaction: Networking supports the entertainment industry by delivering streaming services, online gaming, and social media platforms. It connects people globally, facilitating social interactions and fostering virtual communities.
- Emergency Services and Public Safety: Networking is essential for emergency services like 911 and disaster management. It enables quick communication and coordination during crises, potentially saving lives.
- Education and E-Learning: Networking is a cornerstone of online education and e-learning platforms. It has made education accessible to individuals of all ages, locations, and backgrounds, promoting lifelong learning.
- Global Connectivity: Networking has bridged geographical and cultural gaps, fostering global connectivity. It promotes cross-cultural understanding, trade, and diplomacy.
In summary, networking is important because it underpins modern communication, information sharing, and collaboration. It empowers individuals, businesses, and societies to connect, innovate, and thrive in an increasingly digital world.
The Internet: A Global Network
The internet’s inception marked a turning point in human history, connecting people, businesses, and governments across the globe. ISPs act as gatekeepers, providing access to the internet. They play a pivotal role in ensuring the internet’s availability and reliability.
Challenges and Security in Networking
- Security Threats
- Malware: Malicious software, including viruses, worms, and Trojans, can infect networked devices, steal data, or disrupt network operations.
- Hackers and Intruders: Unauthorized individuals or groups may attempt to gain access to a network for various malicious purposes, such as data theft, espionage, or disruption of services.
- Phishing: Phishing attacks involve tricking users into revealing sensitive information, such as usernames and passwords, by posing as legitimate entities.
- Denial of Service (DoS) and Distributed Denial of Service (DDoS) Attacks: These attacks flood a network or server with traffic, overwhelming it and causing it to become inaccessible to legitimate users.
- Data Privacy
- Data Breaches: Unauthorized access to sensitive data can result in data breaches, leading to financial losses and damage to an organization’s reputation.
- Data Encryption: To protect data in transit, encryption is used to scramble data so that it’s unreadable to anyone without the appropriate decryption key.
- Network Vulnerabilities
- Software Vulnerabilities: Networked devices and software often have security flaws that hackers can exploit. Regular software updates and patch management are essential to address these vulnerabilities.
- Weak Authentication: Weak or default passwords make it easier for attackers to gain unauthorized access to networked devices and services.
- Insider Threats
- Insider Attacks: Employees or individuals with privileged access to a network may misuse their privileges intentionally or unintentionally, posing a significant security risk.
- Social Engineering: Attackers may manipulate individuals within an organization to disclose sensitive information or perform actions that compromise security.
- Network Complexity
- Complexity: As networks grow and become more complex, managing and securing them becomes increasingly challenging. This complexity can lead to misconfigurations and security oversights.
- Legacy Systems: Older systems and devices may lack modern security features, making them susceptible to attacks.
- Mobile and Remote Devices
- BYOD (Bring Your Own Device): The practice of employees using personal devices for work purposes introduces security risks, as these devices may not have the same level of security as company-owned devices.
- Remote Work: The shift to remote work has increased the attack surface, as remote employees access networks and data from various locations and devices.
- Cloud Security
- Cloud-Based Services: Organizations are increasingly using cloud-based services, which require robust security measures to protect data stored in the cloud.
- Shared Responsibility Model: Understanding the division of security responsibilities between cloud providers and users is essential to ensure comprehensive protection.
- Compliance and Regulations
- Data Protection Laws: Organizations must comply with data protection regulations and standards, such as GDPR (General Data Protection Regulation) and HIPAA (Health Insurance Portability and Accountability Act), which impose strict security and privacy requirements.
- Network Monitoring and Detection
- Security Monitoring: Continuous monitoring of network traffic and activities is essential to detect and respond to security incidents promptly.
- Intrusion Detection and Prevention Systems (IDPS): These systems help identify and mitigate threats by monitoring network traffic for suspicious patterns.
- Disaster Recovery and Business Continuity
- Disaster Preparedness: Having a robust disaster recovery plan is critical to ensure network resilience in the face of natural disasters, cyberattacks, or other emergencies.
The Role of Networking in Everyday Life
From online shopping to remote work and telemedicine, networking has reshaped the way we live, work, and connect with others.
FAQs
Computer networking’s primary purpose is to facilitate communication and data exchange between devices and users.
LANs cover smaller geographic areas like buildings, while WANs span larger areas like cities or continents.
Common network devices include routers, switches, modems, and access points.
Network security is crucial for protecting sensitive data, preventing cyberattacks, and ensuring the integrity of networked systems.
Networking has revolutionized the way we work, communicate, and access information, making our lives more convenient and connected than ever before.