Table of Contents
What is TLS?
TLS stands for Transport Layer Security and is a cryptographic protocol that provides secure communication over a computer network. It ensures data privacy, integrity, and authenticity between two endpoints.
As a protocol standardized by the Internet Engineering Task Force (IETF), Transport Layer Security (TLS) ensures the confidentiality, authenticity, and integrity of information passed between programs. It’s the most extensively used security protocol currently available, making it an excellent choice for web browsers and other programs that need to exchange data across a network safely.
Internet connections, file transfers, VPN links, remote desktop connections, and VoIP calls all fall under this category. Recently, TLS has been included in cutting-edge cellular transport technologies like 5G to secure vital RAN functions.
What is TLS in networking
In networking, TLS serves as a crucial layer of security that operates just above the transport layer. It encrypts data transmissions, making them indecipherable to anyone intercepting the communication. TLS is commonly used to secure web traffic, emails, and various other types of data exchange on the internet.
How does TLS work?
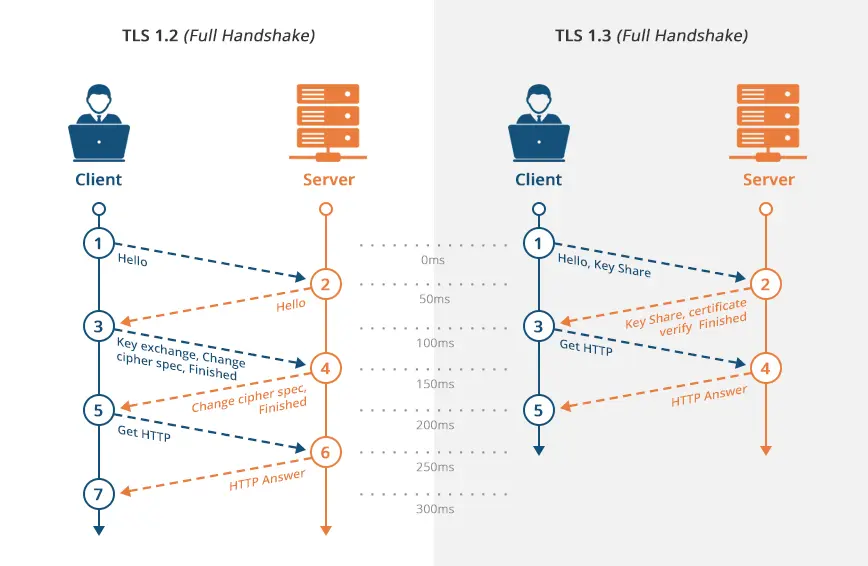
TLS employs symmetric and asymmetric encryption techniques to establish a secure connection between a client (your device) and a server (a website or service). It begins with a process known as the TLS handshake, during which the client and server agree on encryption parameters and exchange cryptographic keys. This handshake ensures that subsequent data exchanges are protected.
When two devices, such as a client and a server, want to establish a secure connection, they initiate a TLS handshake. This handshake involves a series of steps:
- Client Hello: The client sends a message to the server, indicating its supported TLS versions, encryption algorithms, and other parameters.
- Server Hello: The server responds with its chosen TLS version, encryption algorithm, and other parameters.
- Certificate Exchange: The server presents its digital certificate to the client, which contains the server’s public key.
- Key Exchange: The client and server agree on a shared secret key that will be used for encrypting and decrypting the data.
- Establish Secure Connection: Finally, the client and server use the shared secret key to encrypt and decrypt the data transmitted between them.
The benefits of Transport Layer Security
When comparing the advantages of using TLS with those of not using it, they are obvious. Data encryption, integrity checks, and a secure authentication mechanism are all made possible via a TLS-encrypted session. While Internet Protocol Security (IPsec) is also a secure authentication and encryption protocol suite, TLS has advantages that have led to its replacement in many enterprise deployments. The following are some of the advantages:
- Data Confidentiality: TLS encrypts data, making it unreadable to eavesdroppers.
- Data Integrity: It ensures that data remains unaltered during transmission.
- Authentication: TLS verifies the authenticity of the server, preventing man-in-the-middle attacks.
- Compatibility: TLS is widely supported and compatible with various protocols and applications.
- Trust: The use of TLS certificates builds trust with users, assuring them of a secure connection.
The Difference Between TLS and SSL
TLS and SSL (Secure Sockets Layer) are both cryptographic protocols that provide secure communication over a network. The main difference between the two is their versions. SSL was the predecessor of TLS and has been deprecated due to security vulnerabilities. TLS versions 1.0, 1.1, 1.2, and 1.3 have been developed to address these vulnerabilities and improve security.
| Aspect | TLS (Transport Layer Security) | SSL (Secure Sockets Layer) |
|---|---|---|
| Protocol Purpose | Provides secure communication over a computer network. | Provides secure data transmission between a client and a server. |
| Security Evolution | Evolved from SSL to address vulnerabilities in SSL. | An earlier version of the security protocol. |
| Authentication | Uses digital certificates to verify the authenticity of the server. | Also uses certificates for server authentication. |
| Key Exchange | Employs more secure key exchange algorithms. | Uses less secure key exchange methods. |
| Performance | Generally faster and more efficient than SSL. | Slower and less efficient compared to TLS. |
| Vulnerabilities | Has addressed many vulnerabilities found in SSL. | Prone to several known vulnerabilities. |
| Widely Supported | Widely supported and considered the modern successor to SSL. | Support has diminished, and it’s considered less secure. |
| Versions | Multiple versions, with TLS 1.3 being the latest. | SSL 3.0 is the final version; subsequent versions became TLS. |
| Security Strength | Offers stronger security and encryption. | Encryption is weaker compared to TLS. |
| Recommended Usage | Recommended for securing web traffic, emails, and various network communications. | Not recommended due to known security issues. |
Please note that TLS is the recommended choice for secure communications today, while SSL is considered outdated and less secure due to known vulnerabilities. It’s crucial to use the latest version of TLS for the best security practices.
The Difference Between TLS and HTTPS
HTTPS (Hypertext Transfer Protocol Secure) is a combination of HTTP and TLS. It is the secure version of HTTP and uses TLS to encrypt the data transmitted between a client and a server. While TLS provides the underlying secure communication, HTTPS ensures that websites are accessed securely over the internet.
| Aspect | TLS (Transport Layer Security) | HTTPS (Hypertext Transfer Protocol Secure) |
|---|---|---|
| Definition | Cryptographic protocol for securing data in transit over a network. | A secure version of the HTTP protocol used for secure web communication. |
| Scope of Application | Widely used for securing data transmission in various network protocols and applications. | Specifically designed to secure web communication between a client (browser) and a web server. |
| Encryption | Provides encryption for data transmitted between client and server. | A secure version of the HTTP protocol is used for secure web communication. |
| Authentication | Involves the verification of the server’s authenticity using digital certificates. | Verifies both the server and the website’s identity, assuring users of a secure connection. |
| Browser Indication | Browsers may display a padlock icon or a similar symbol to signify a secure connection when TLS is in use. | Browsers display a padlock icon and often highlight the URL in green to indicate a secure HTTPS connection. |
| Data Integrity | Ensures that data remains unaltered during transmission between client and server. | Provides data integrity by preventing tampering or modification of data during transmission. |
| Port | Typically operates on port 443. | Uses the standard HTTP port (80) for unsecured connections and port 443 for secure connections. |
| Common Usage | Widely used in various network applications beyond web browsing, including email, file transfers, and more. | Exclusively used for securing web communication, making it essential for e-commerce, online banking, and data exchange. |
| Evolution | Evolved from SSL (Secure Sockets Layer) and has multiple versions (e.g., TLS 1.2, TLS 1.3). | Evolved from HTTP and is commonly used with different TLS versions (e.g., TLS 1.2, TLS 1.3). |
| Overall Security | Provides a robust layer of security for data transmission across networks. | Offers a high level of security for web interactions, making it a standard for online security. |
| Key Components | Relies on cryptographic algorithms, keys, and digital certificates for security. | Relies on TLS for encryption, digital certificates, and server authentication. |
| Importance in Web Security | Essential for securing data in various network applications. | Critical for ensuring the security and privacy of user data on websites. |
Both TLS and HTTPS play vital roles in securing digital communication, with TLS providing the underlying cryptographic protocol, and HTTPS being the visible indicator of a secure web connection. Together, they contribute to a safer and more secure online experience.
TLS Encryption Algorithms
TLS supports various encryption algorithms, each with its strengths and weaknesses. Choosing the right encryption algorithm is essential for balancing security and performance in different contexts.
Transport Layer Security (TLS) is a critical component of secure networking. It provides data confidentiality, integrity, and authentication, ensuring that your sensitive information remains secure during transmission. By understanding TLS and its benefits, you can make informed decisions to protect your data and maintain a secure online presence.